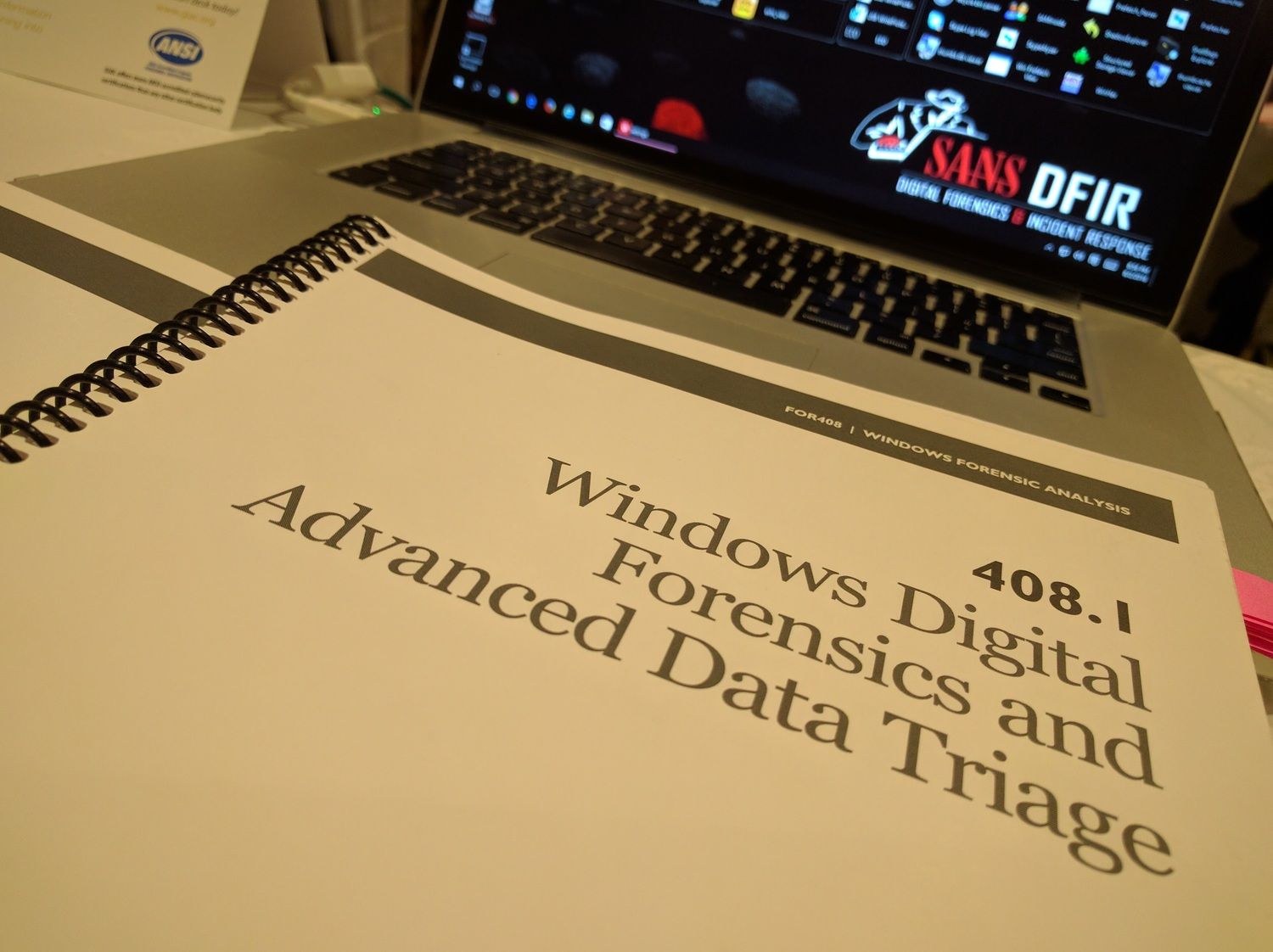
Embracing DFIR W/ SANS FOR408
FOR408: WINDOWS FORENSIC ANALYSIS. Continuing education and furthering one's toolset in their profession is a critical part of anyone's life. An infosec consultant often has to flex across multiple verticals, which is why I'm embracing Digital Forensics and sharing my experience with the SANS FOR408 course.

Why FOR408

Continuing education and furthering one's toolset in their profession is a critical part of anyone's life. An information security (infosec) consultant often has to be agile across multiple verticals, which is why I am embracing Digital Forensics. I took a digital forensics course in school, but as my fellow undergrads can attest, a single college class does NOT prepare you for work. College focuses on principles, comprehension, and understanding of concepts—not the in-depth "actions on" with the tools, procedures, and industry best practices. Another inevitability for an infosec consultant is collecting certifications. When you pair the two, I guarantee you run into the word SANS somewhere in that conversation. That's why Windows Forensic Analysis (FOR408) was the right course for me. It is their introductory course within the Digital Forensics & Incident Response arm of the institute. This post is by no means a commercial for SANS because SANS is not paying me a dollar; I'm simply sharing my experience.
What to Expect
Currently, Windows Forensic Analysis is a six-day course covering the Windows operating system, spanning from Windows XP to the most recent Windows 10 release. The course gives you a view of the operating system that most won't see. It educates you on what's happening behind the scenes along with the tools, tactics, and procedures veterans in the field use to accomplish a task.
- DAY 1: WINDOWS DIGITAL FORENSICS AND ADVANCED DATA TRIAGE
- DAY 2: WINDOWS REGISTRY FORENSICS AND ANALYSIS
- DAY 3: USB DEVICES, SHELL ITEMS, & KEY WORD SEARCHING
- DAY 4: EMAIL, KEY ADDITIONAL ARTIFACTS, AND EVENT LOGS
- DAY 5: BROWSER FORENSICS: FIREFOX, INTERNET EXPLORER & CHROME
- DAY 6: WINDOWS FORENSIC CHALLENGE
How the Course Runs
The first day you cover the basics of forensics in the context of capturing images. A unique aspect of day one is learning to lean on triage. If you know anything about forensics, the usual practice is to take a full disk image of the box. When time is of the essence, you can create a triage image by grabbing specific pieces of the machine to analyze and answer pressing questions quickly. Afterward, for due diligence, you still do the full disk image. "It is a method."
The course ends when you put it all into action. There is a challenge that reinforces the material throughout the week. You team up with your peers in the class and work a forensics case. You receive an image, a scenario, and you FORENSICATE. At the end of the time allotted, you present your findings to your peers and they vote on the best presentation of the facts.
Favorite Parts of FOR408
There are exercises throughout the course that reiterate what was explained in a section. I enjoyed learning the manual process of analyzing artifacts, where they live, and which areas matter. After doing that, the instructors reveal the tool that does a lot of the heavy lifting for you. So many organizations, courses, and workshops just tell you to run the tool and let the magic happen, and you never learn what it's doing. When you operate that way, you really can't explain to an audience what happened and how the data came to be.
Tips and Takeaways
There is a lot of information to acquire and only six days to do it. On Day 6, while you have assistance, you are basically performing. Many people in the course hit that saturation point where their brain felt like it was about to explode from forensic artifacts flying by section after section. Another parallel aspect to watch for is limiting distractions during the course. If you lose focus on the material, you might miss an incredibly important piece that could set you back 30 minutes to an hour on an issue you could have solved with a single click in an interface.

Digital Forensics and Incident Response is a critical piece that organizations should prepare for and at Rendition InfoSec it is a cornerstone of what we do. Excellent course to take and it can prepare you for the next week going out and applying the procedures to real forensic and incident response cases. Before you know it you will be among the other DFIR professionals in the community contributing back to others that want to learn about forensics in the future. Just remember there is more than one way to get to a conclusion and this course might not be right for everyone, but there are many shadow copies out there that you can get something out of. ;-)
If you decide that you are interested in taking this course more information can be found here.
Keep reading
View archiveBuilding Mission Control Playbooks
How automation, AI copilots, and clear decision loops shorten the distance between detection and response.
Here's one way I check for malicious IPs
AbuseIPDB is a project dedicated to helping combat the spread of hackers, spammers, and abusive activity on the internet. Here's a tool I wrote to query their API and data base of malicious IPs.
Speaking to Rooms Where You're Not the Expert
What I learned preparing to facilitate AWS CISO Circle discussions in Bangkok and Singapore during the week of Black Hat Asia 2026: senior rooms need perspective, questions, and facilitation more than another expert monologue.