Tag
General
Curated writing exploring general across security strategy, operations, and tooling.

Website and Blog Redesign
Today I’m launching a redesigned, integrated michaelbanks.org experience that brings my website and blog together into one platform.

Relaunching michaelbanks.org
Design goals, architecture decisions, and how I'm preparing the site for AI-assisted publishing.

How I got started and my journey in Cybersecurity
Recently I was extended an opportunity to speak at an undergraduate class of computer science. The topic I was to speak on was how I got into cybersecurity and my experience of different roles within the public and private sector of cybersecurity. I thought I'd share my story...
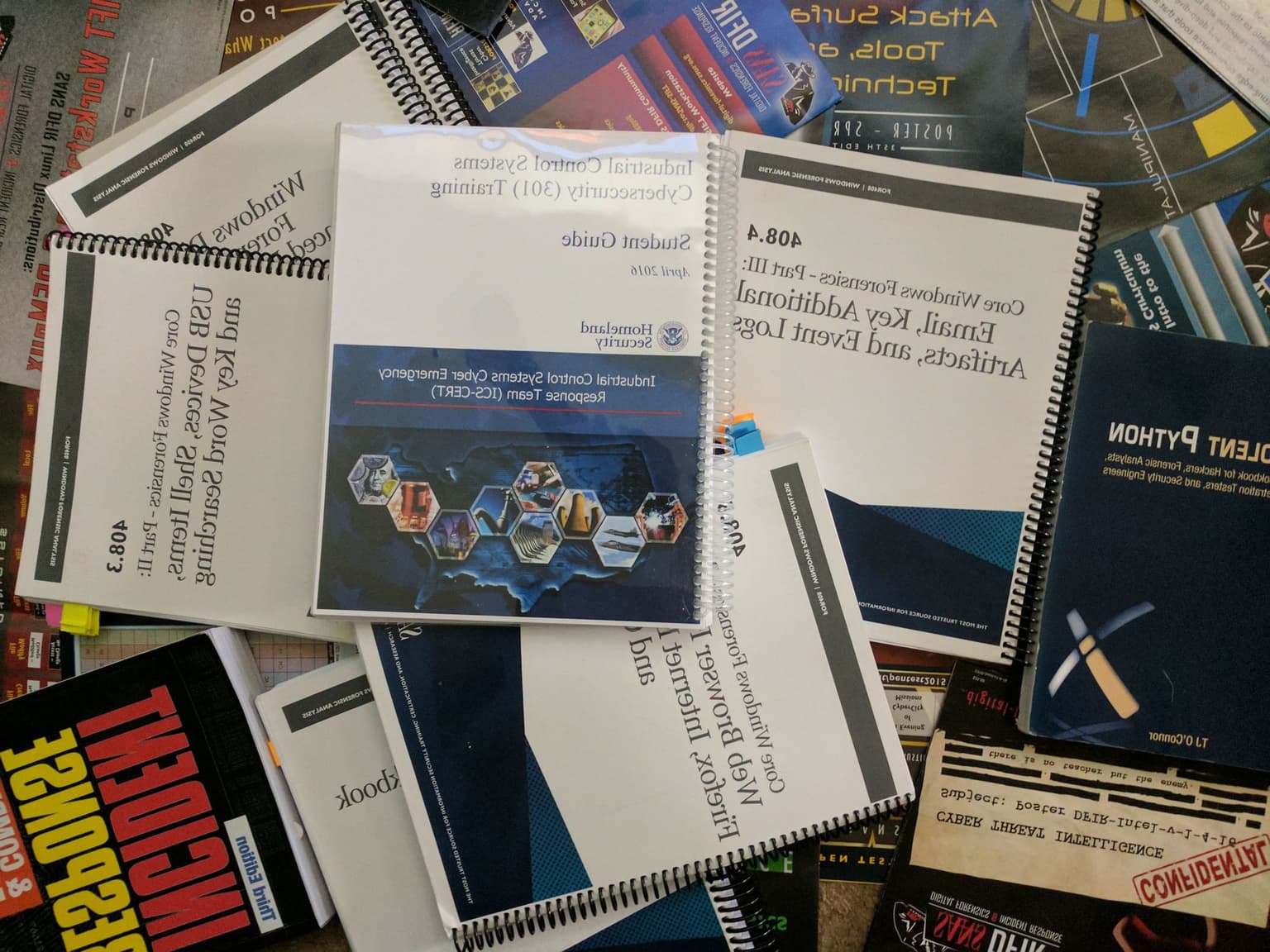
The 5 Books Every Cybersecurity Professional Should Read
A group of industry professionals that I know started to talk about interesting books they've read and thus own our very own cyber book club began. Now I keep track of a running and ever-evolving list of books that I genuinely believe EVERYONE in the field and industry should...
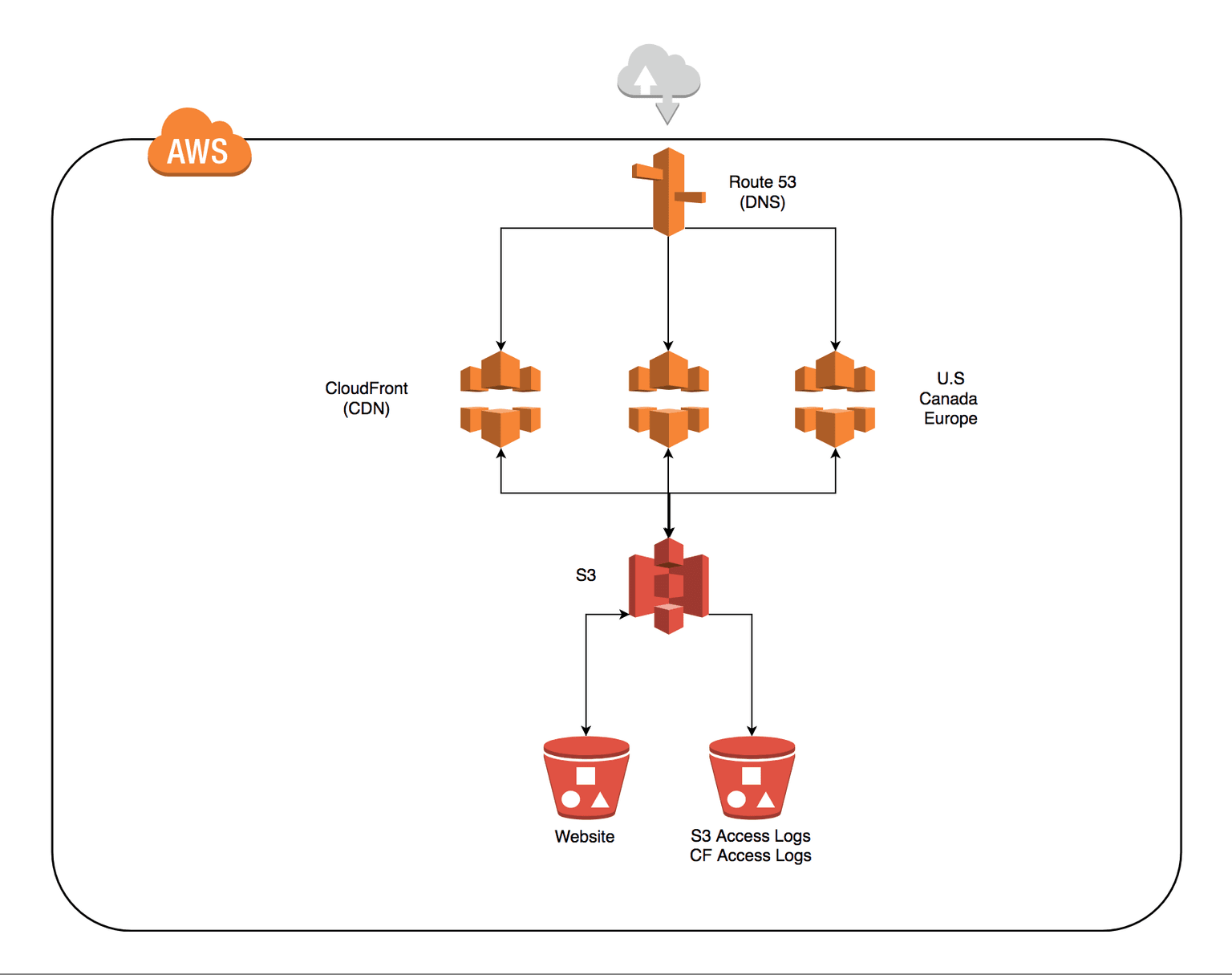
This is My Architecture
Like all things in our industry, things change and evolve. Years ago, I started a personal website. I believe everyone should have a presence somewhere that explains who you are and what you do.
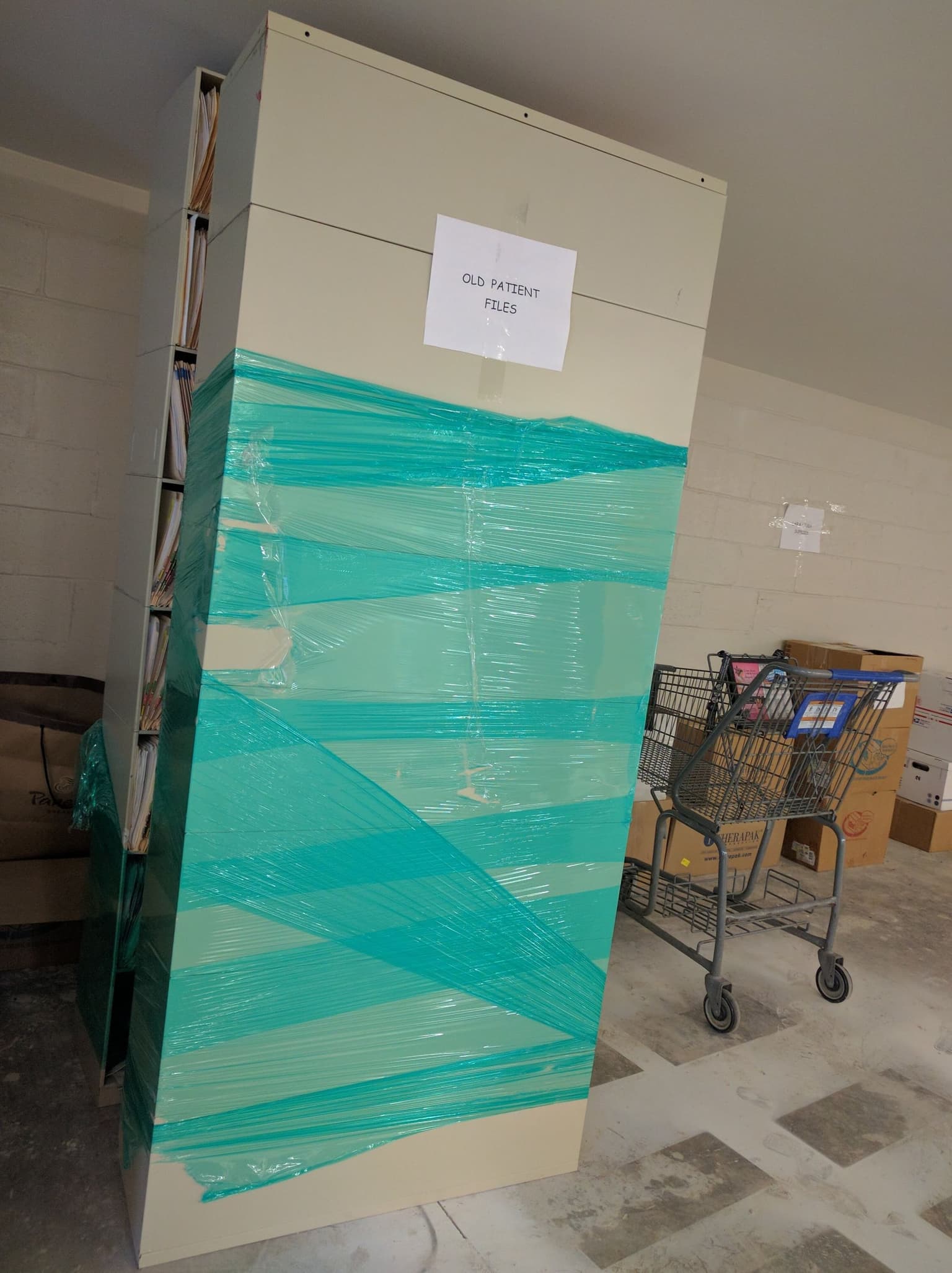
Please Don't Be Like These Guys
With the inevitable breaches that hit the news regularly, I often find myself asking: "What exactly are companies doing to protect our data?"

A Year In The Life
This has been just an amazing year. I have flown about 50,000 miles (47,820) in the sky on an airplane and got to see so much of the US in a short amount of time. I have spent 101 days on the road and have stayed in many Marriotts and Hiltons.
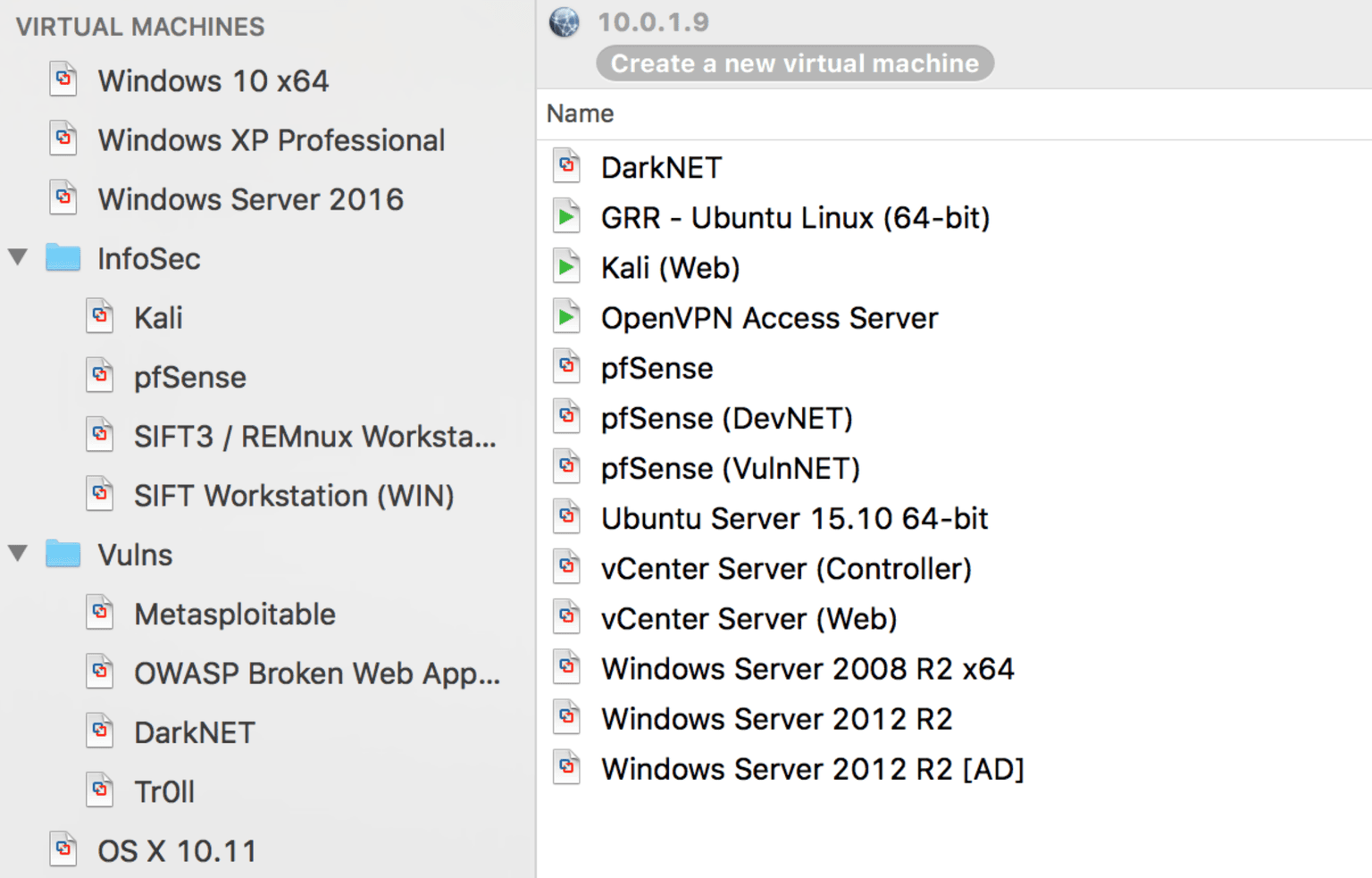
What's In Your Lab?
There come times when an Information Security Consultant may have to deal with a program, vulnerability, or even an operating system you haven't touched before. For moments like that, an essential item in a consultant's toolbox needs to be utilized: a lab.

Project Slam
Project Slam is an initiative to utilize tools to aid in defending against nefarious adversaries. The overall focus is to research adversary’s behavior and utilize the data to generate wordlists and expose methodologies of various threat actors that can be provided back to the...
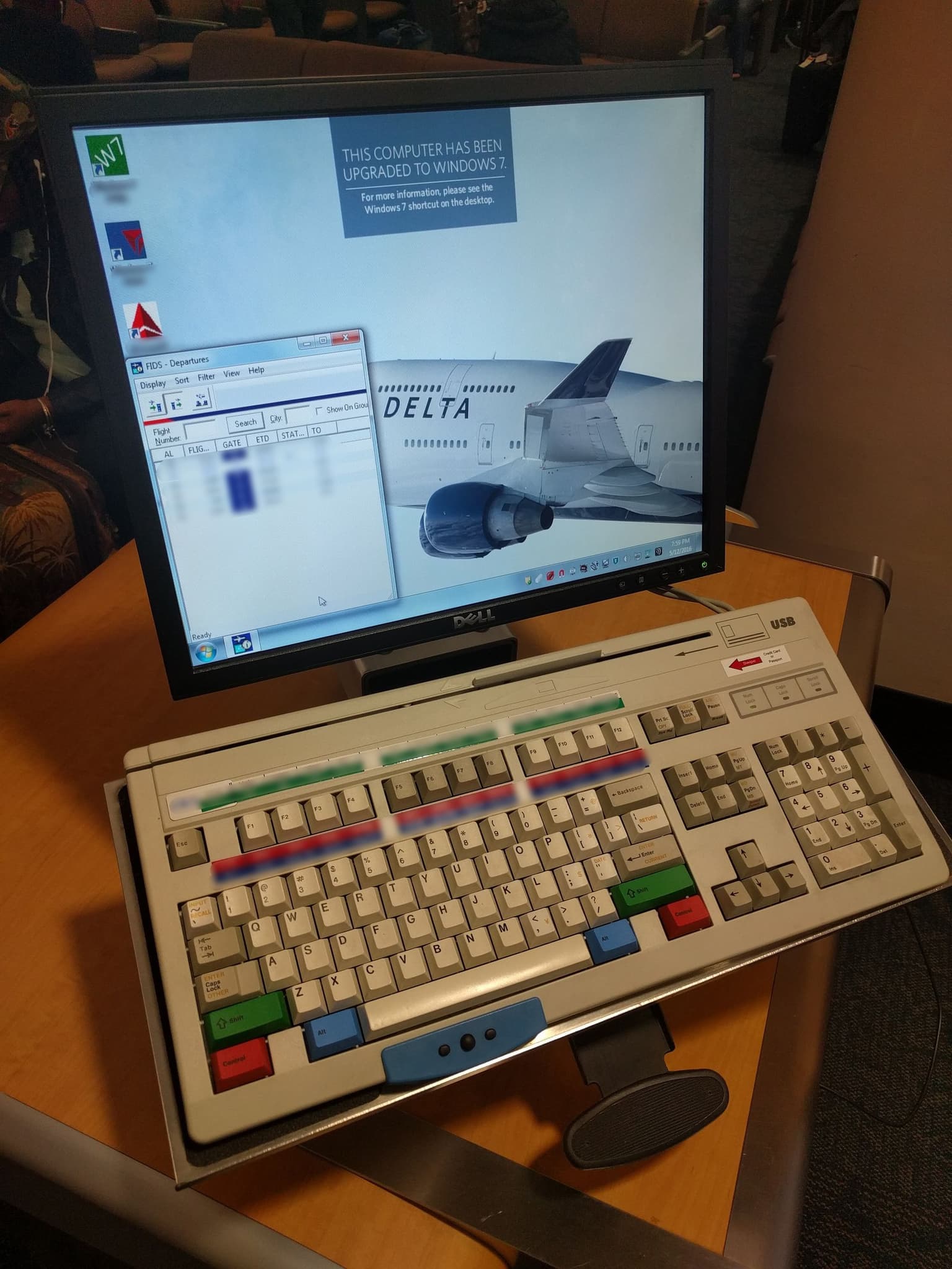
5 Tips Airports Should Probably Pay Attention To
While being at the airport a lot, you tend to end up noticing some not so flattering things. In general, it's been my experience that all airports have issues.